Protecting your NFC (Near Field Communication) tag involves taking measures to prevent unauthorized access or tampering. Here are some tips to help you protect your NFC tag:
Password Protection:
If your NFC tag supports password protection, enable it. This adds an additional layer of security by requiring a password or PIN to access the information on the tag.
Read-only Mode:
Set your NFC tag to read-only mode if possible. This prevents anyone from writing new data to the tag, protecting the existing information.
Use Encryption:
If the information on your NFC tag is sensitive, consider encrypting it. Encryption adds a layer of security by scrambling the data, making it unreadable without the appropriate decryption key.
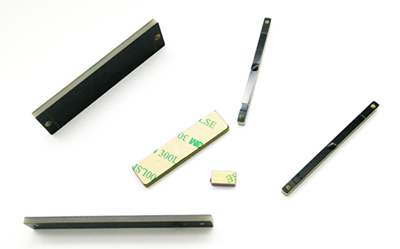
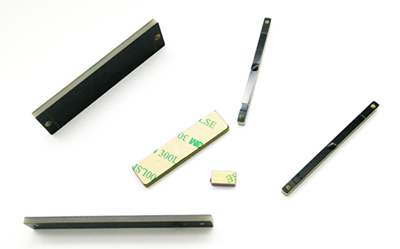
Choose a Secure NFC Tag Type:
Different NFC tag types have varying levels of security features. Choose a tag type that suits your security needs. For example, some NFC tags have built-in security features like mutual authentication.
Physical Protection:
Shield your NFC tag from physical damage. Place it in a durable and secure location to prevent it from being easily removed, damaged, or tampered with.
Limit Access:
Control physical access to the NFC tag. If the tag is embedded in an object, ensure that only authorized individuals have access to that object.
Use Anti-Tamper Features:
Some NFC tags come with anti-tamper features that can trigger an alert if someone tries to tamper with the tag. Explore NFC tags with features like digital seals or sensors that detect physical tampering.
Secure Data on the Server:
If the NFC tag links to data stored on a server, make sure the server is secure. Implement strong authentication mechanisms and encryption for data transmission between the NFC tag and the server.
Regularly Monitor and Update:
Regularly monitor the use and status of your NFC tags. If any unauthorized access is detected, take appropriate actions, such as updating passwords or replacing compromised tags.
Educate Users:
If multiple people have access to the NFC tags, educate them on the importance of security measures and best practices. This includes not sharing passwords and being cautious about where and how the tags are used.
Remember that the level of protection required depends on the sensitivity of the information stored on the NFC tag. Assess your specific needs and implement a combination of these measures to enhance the security of your NFC tags.